Cybersecurity is often portrayed as dramatic. Headlines scream about breaches. Dashboards flash red. Incident response teams scramble.
But long before an incident unfolds, there is quieter work taking place. Structured work. Methodical work. Preventive work.
That work is vulnerability assessment and management.
A comprehensive course in Vulnerability Assessment and Management does far more than teach you how to run scanners. It reshapes how you think about systems, risk, exposure, and accountability. It develops technical capability, yes—but also strategic judgment. Below is a deep exploration of what you truly gain from such a course and how it transforms your professional skill set.
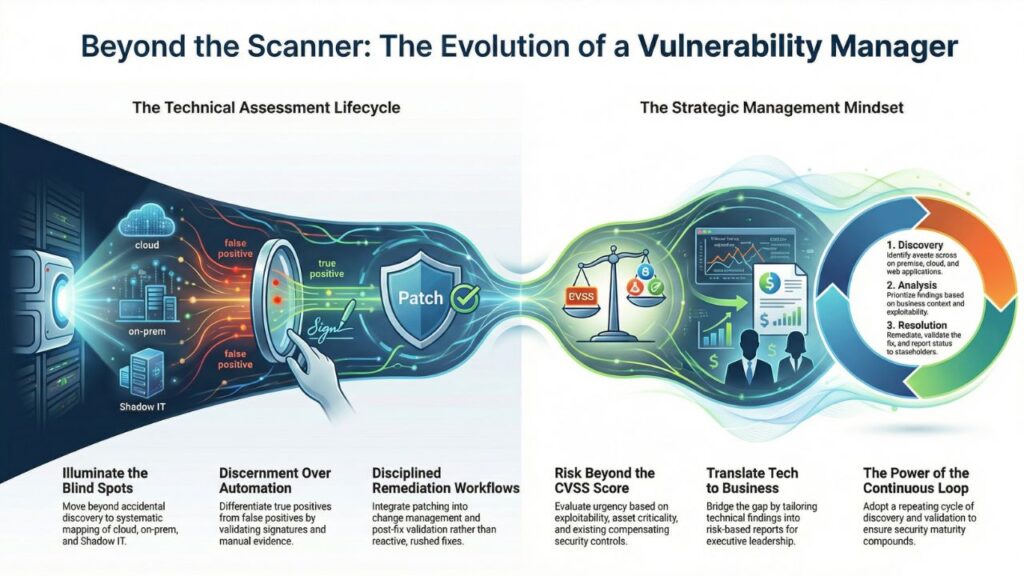
1. You Learn to See What Others Overlook
Security begins with visibility.
One of the most foundational lessons in vulnerability management is deceptively simple: you cannot secure what you cannot see. The course trains you to approach environments with disciplined curiosity. You learn how to identify assets across on-premise infrastructure, cloud workloads, and web applications. Servers. Databases. APIs. Shadow IT. Forgotten development systems.
Discovery becomes systematic rather than accidental.
You understand how host discovery works. You learn port enumeration techniques. You analyze service banners. You recognize patterns in network responses. Suddenly, infrastructure is no longer abstract—it is mapped, categorized, and understood.
This shift alone is transformative. Many security gaps stem not from negligence, but from incomplete visibility. The course teaches you to illuminate blind spots.
2. You Develop Technical Depth in Scanning and Enumeration
Running a vulnerability scanner is easy. Interpreting it is not.
A well-designed course teaches the mechanics of scanning—how tools perform checks, what signatures mean, how service detection works, and how web application scanners evaluate configurations. But more importantly, it teaches discernment.
Not every alert is real.
Not every finding is exploitable.
Not every severity score reflects business risk.
You learn to differentiate between true positives and false positives. You validate findings manually. You confirm versions. You inspect configuration files. You cross-check evidence.
This analytical rigor separates a practitioner from an operator. You no longer accept tool output blindly. You verify. You challenge. You substantiate.
And that skill is invaluable.
3. You Understand Risk Beyond CVSS Scores
Many beginners assume that vulnerability management is about sorting by severity and patching everything labeled “Critical.”
Reality is more nuanced.
A key lesson from the course is contextual risk evaluation. A critical vulnerability on an isolated lab server does not carry the same urgency as a high-severity issue on a customer-facing payment portal.
You learn to incorporate multiple dimensions into risk assessment:
- Exposure level (internal vs. internet-facing)
- Exploitability (is there public exploit code?)
- Asset criticality (business function and data sensitivity)
- Compensating controls (WAF, network segmentation, EDR coverage)
- Compliance requirements
This multidimensional evaluation sharpens your judgment. Risk becomes a business conversation—not just a technical metric.
You begin to think like a security strategist rather than a scanner operator.
4. You Master Prioritization Under Constraints
Time is limited. Resources are finite. Teams are stretched.
The course teaches prioritization frameworks that bring structure to chaos. Instead of reacting emotionally to the loudest issue, you evaluate risk systematically and allocate remediation effort where it matters most.
You might build scoring models. You might adopt tier-based classification. You might align remediation timelines with risk severity.
The point is not the model itself—it is the mindset. You learn to make defensible decisions.
And in enterprise security, defensibility matters.
5. You Learn Remediation as a Process, Not an Afterthought
Finding vulnerabilities is only half the equation. Closing them is where maturity is measured.
A vulnerability management course emphasizes structured remediation workflows:
- Patch identification
- Testing in non-production environments
- Change management approvals
- Deployment scheduling
- Post-fix validation scans
You understand why rushed patching can cause outages. You appreciate the importance of configuration hardening. You learn how secure baselines prevent recurring weaknesses.
Security becomes integrated into operational processes rather than bolted on.
This shift—from reactive patching to disciplined lifecycle management—is one of the most significant skill upgrades you gain.
6. You Build Validation Discipline
A vulnerability marked “fixed” is not automatically resolved.
You learn the importance of verification. Post-remediation scans confirm that patches were applied correctly. Manual re-testing ensures the vulnerability is no longer exploitable. Configuration reviews validate intended changes.
This validation discipline strengthens credibility.
When you report that a risk has been mitigated, leadership can trust that statement. Auditors can rely on your documentation. Stakeholders can make informed decisions.
In security, trust is built on evidence.
7. You Learn to Translate Technical Findings into Business Language
One of the most underrated skills in cybersecurity is communication.
A vulnerability assessment report filled with raw technical jargon is rarely useful to executives. A well-structured report that connects risk to business impact is powerful.
The course trains you to create consolidated reports that include:
- Vulnerability description
- Severity rating
- Affected systems
- Business impact
- Recommended remediation
- Validation status
More importantly, it teaches you to tailor reporting for different audiences. Engineers need technical depth. Management needs risk summaries. Auditors require traceability.
You learn how to bridge those perspectives.
That ability elevates your professional value significantly.
8. You Gain Governance and Compliance Awareness
Vulnerability management does not operate in isolation. It often supports regulatory frameworks and compliance standards.
Through the course, you understand how structured scanning, documentation, and remediation tracking align with audit expectations. You see how consistent reporting demonstrates control effectiveness.
This governance awareness enhances your career trajectory. You move beyond tool usage and begin to understand policy alignment, audit defensibility, and regulatory posture.
You become a contributor to organizational resilience—not just technical hygiene.
9. You Internalize the “Repeat” Principle
Perhaps the most important lesson is cyclical thinking.
Security is not a one-time project. Infrastructure evolves. New software is deployed. Configurations change. Threat actors innovate.
Vulnerability management is continuous.
Discover.
Analyze.
Prioritize.
Remediate.
Validate.
Report.
Repeat.
The repetition is deliberate. It ensures that security posture improves incrementally rather than stagnating. It reinforces operational discipline. It embeds security into routine practice.
Without repetition, progress decays.
With repetition, maturity compounds.
10. You Develop Analytical Thinking
Beyond tools and workflows, the course sharpens analytical reasoning.
You begin asking better questions:
- Why is this service exposed?
- Who owns this asset?
- What business function does it support?
- Is this vulnerability exploitable in our environment?
- What is the downstream impact if exploited?
This structured inquiry becomes instinctive. You approach systems methodically. You evaluate assumptions. You identify hidden dependencies.
Such analytical depth extends beyond vulnerability management. It enhances your performance in architecture reviews, cloud security, application security, and incident response.
11. You Strengthen Professional Confidence
Confidence in cybersecurity does not come from memorizing tools. It comes from understanding processes.
When you know how discovery works, how scanning logic functions, how risk is contextualized, and how remediation is validated, you operate with clarity.
You are not intimidated by complex environments.
You are not overwhelmed by long scanner reports.
You are not reactive under pressure.
You are methodical.
That confidence is earned through structured learning.
12. You Build a Security-First Mindset
Perhaps the most profound transformation is philosophical.
You begin to see vulnerabilities not as isolated defects but as symptoms of systemic weaknesses—outdated processes, poor configuration management, insufficient oversight, or inconsistent patch cycles.
Security becomes cultural rather than technical.
You advocate for baseline hardening.
You encourage asset inventories.
You support change management rigor.
You promote continuous scanning.
Your perspective expands.
13. You Enhance Career Mobility
Vulnerability management intersects with multiple cybersecurity domains:
- Infrastructure Security
- Cloud Security
- Web Application Security
- Governance, Risk, and Compliance
- Security Operations
The skills you gain are transferable. They strengthen your resume. They improve interview performance. They demonstrate operational understanding.
Employers value professionals who can identify risk, prioritize intelligently, and communicate clearly. This course builds exactly those competencies.
14. You Learn Practical, Repeatable Methodologies
The most effective courses avoid abstract theory. They teach practical workflows you can replicate in real environments.
You leave with:
- A structured assessment approach
- A scanning methodology
- A risk prioritization framework
- A remediation lifecycle model
- A reporting template
These are not academic concepts. They are operational tools.
And they remain relevant across industries.

15. You Embrace Continuous Improvement
Finally, you internalize that perfection is unrealistic—but improvement is achievable.
Every assessment uncovers gaps. Every remediation cycle strengthens posture. Every reporting cycle refines metrics.
Vulnerability management is iterative maturity.
It is about reducing attack surface gradually.
It is about lowering risk incrementally.
It is about building resilience systematically.
That philosophy extends beyond security. It fosters disciplined growth in any professional domain.
Conclusion: More Than a Course
A Vulnerability Assessment and Management course is not simply a technical training program. It is a structured introduction to disciplined risk governance.
You learn to see clearly.
You learn to analyze critically.
You learn to prioritize intelligently.
You learn to remediate responsibly.
You learn to communicate strategically.
You learn to repeat relentlessly.
In doing so, you evolve from someone who runs tools into someone who manages risk.
And in modern cybersecurity, that distinction makes all the difference.